Services / AI Agents & MCP
AI agents and MCP servers built for production
Agentic AI systems and Model Context Protocol (MCP) servers with authentication boundaries, audit logging, and security testing from day one. Agents that reason, call tools safely, and survive investor diligence.
Fit check
You're a fit if…
Production stakes
Agents will touch real systems (billing, support, data pipelines) and must be auditable with rollback and RBAC.
Retrieval + tools
You need semantic search/RAG plus tool calls in one flow, with clear tenant filters and schema validation.
One owner
You want architecture diagrams, MCP server code, and security testing handled by the same team.
When you actually need agents
AI agents are LLM-powered workflows that keep state, call tools, and make decisions across multiple steps. They aren't always the right fit — simple prompts often work. Agents make sense when you need:
- Multi-step workflows where a single prompt can't manage state or secure MCP tool usage
- Human-in-the-loop approvals with audit trails
- Chained RAG retrieval, tool execution, and policy checks without brittle scripts
- Long-running processes (hours/days) orchestrated across tasks
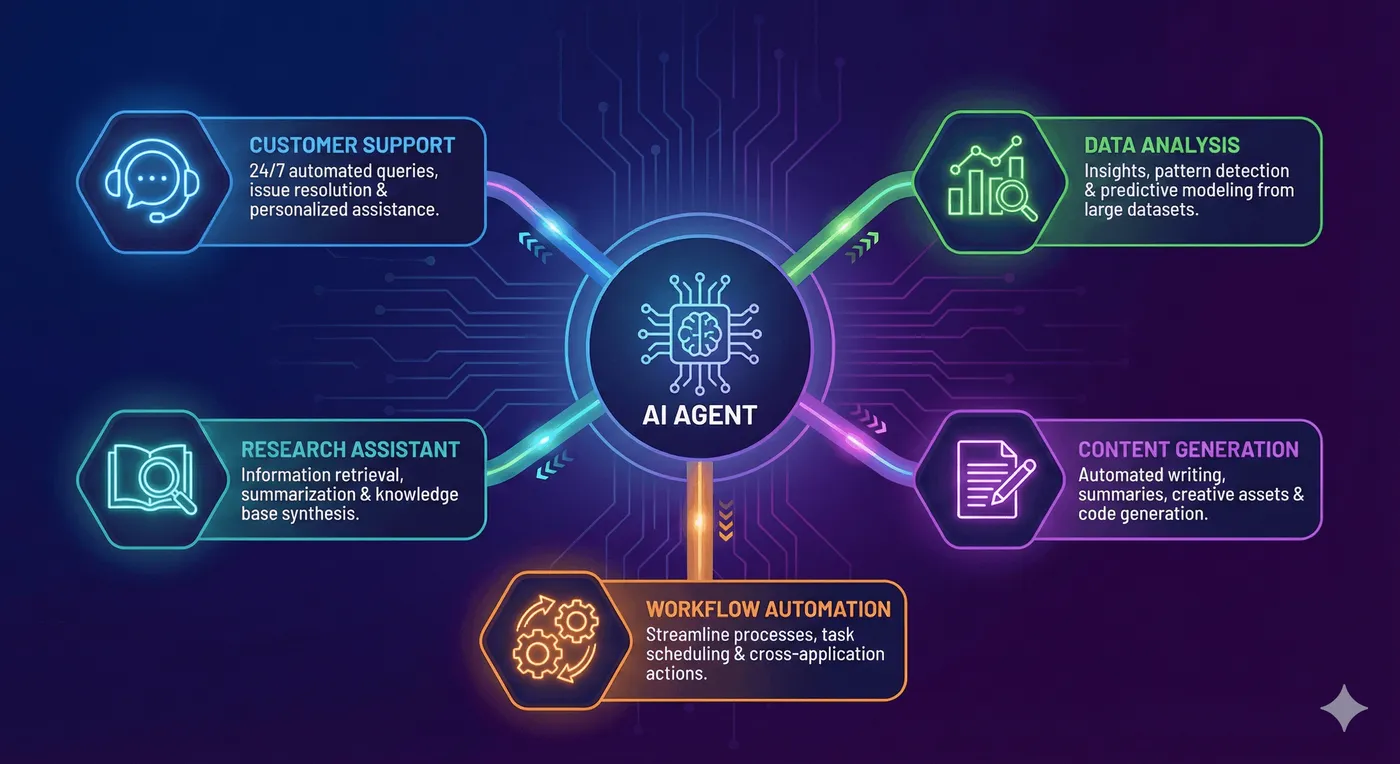
Use cases we build
How we build agents & MCP servers
Typed tools, rate limiting per tenant, runtime sandboxes, and audit logging make MCP servers production-ready.
- 1. Workflow mapping. Identify user journeys, desired automation, and human-in-the-loop steps.
- 2. Tool surface design. Define MCP tools/functions, schemas, auth scopes, and failure modes.
- 3. Build & guard. Implement agents, prompts, tool servers, and guardrails. Wire logging + alerts.
- 4. Hardening & rollout. Prompt-injection testing, pen tests, telemetry dashboards, and staged rollout.
Technical stack
Next.js with App Router, Vercel Edge for low-latency routing, Postgres + pgvector for agent memories, Redis/Upstash for queues, Docker sandboxes for code execution, PostHog for every tool invocation. LangChain, Anthropic Claude, OpenAI, and custom orchestrators all wired with RBAC, logging, and guardrails.
Our security testing applies to every MCP server — we attack tool definitions with malicious prompts, test privilege escalation, and validate audit logs.
Case study
Multi-tenant MCP API platform
Built a multi-tenant SaaS platform with MCP server integration, Clerk authentication, rate limiting, and production infrastructure on Vercel with comprehensive security testing.
Technical challenges
- Row-level security for multi-tenant data isolation
- Redis rate limiting per tenant + per tool
- MCP server integration with typed auth boundaries
Key outcomes
- 2,000+ automated tests from the first sprint
- Auth boundaries prevent tenant data leakage
- Zero-downtime production deployment
8 weeks
Build time
2,000+
Security tests
Multi-tenant
Architecture
Common questions
Learn more about AI agents
Explore our tools, read in-depth guides on agent architecture, or get in touch to discuss your use case.
